
|
||||||
Name of Your Organization:
Blue Lane Technologies
Web Site:
www.bluelane.com
Compatible Capability:
Blue Lane PatchPoint System
Capability home page:
http://www.bluelane.com/product/index.html
Compatible Products
|
|||
General Capability Questions
1) Product Accessibility <CR_2.4>
Provide a short description of how and where your capability is made available to your customers and the public (required) :
The PatchPoint System is the only inline patch proxy for enterprise servers that checks for the same conditions and applies the same corrective action as the software vendor security patch to fix application-specific vulnerabilities at the root cause. The PatchPoint Gateway is a scalable, high-performance appliance that monitors client/server interactions, verifies the existence of vulnerabilities and applies corrective action inline by emulating software vendor security patches.
Mapping Questions
4) Map Currency Indication <CR_5.1>
Describe how and where your capability indicates the most recent CVE version used to create or update its mappings (required) :
Our product is focused on vendor patches and each patch has corresponding CVE/CAN numbers associated with it. In our product we expose only the patches and their mapping to CVE/CAN numbers, but do not expose the user to the CVE version information. All CVE references in our product link to the Mitre-CVE database where up to date versions of the CVE data is held.
Updates to our build process occurs on a bi-weekly basis, at which time we are updating our CVE number mappings. Also on a bi-weekly basis our customers get updates to this information as appropriate to our product.
5) Map Currency Update Approach <CR_5.2>
Indicate how often you plan on updating the mappings to reflect new CVE versions and describe your approach to keeping reasonably current with CVE versions when mapping them to your repository (recommended) :
We remain current with the latest Mitre-CVE database on a bi-weekly basis, where new "ActiveFixes" (our products content carrying CVE information) are updated via an automated web-based tool.
6) Map Currency Update Time <CR_5.3>
Describe how and where you explain to your customers the timeframe they should expect an update of your capability's mappings to reflect a newly released CVE version (recommended) :
On a bi-weekly basis, our database of CVE to patch mappings is updated for all of our customers.
Documentation Questions
7) CVE and Compatibility Documentation<CR_4.1>
Provide a copy, or directions to its location, of where your documentation describes CVE and CVE compatibility for your customers (required) :
Explanation: PatchPoint System Basics Guide: Chapter 5, page 32: "About CVE"
8) Documentation of Finding Elements Using CVE Names <CR_4.2>
Provide a copy, or directions to its location, of where your documentation describes the specific details of how your customers can use CVE names to find the individual security elements within your capability's repository (required):
Usage: PatchPoint System Administrator's Guide: Chapter 3, page 34; Chapter 7, page 65
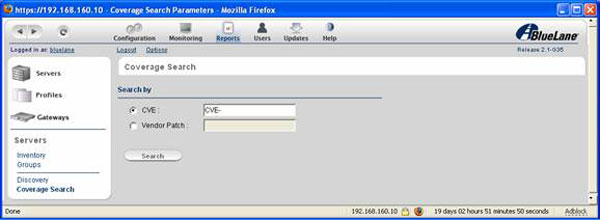
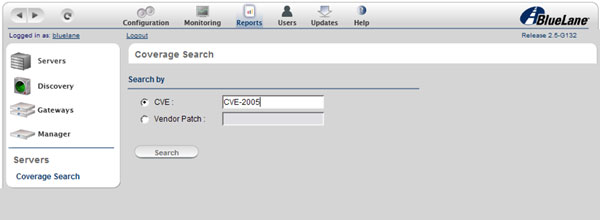
There is a simple mechanism to search via CVEs in our product, below are examples of the search screens:
9) Documentation of Finding CVE Names Using Elements <CR_4.3>
Provide a copy, or directions to its location, of where your documentation describes the process a user would follow to find the CVE names associated with individual security elements within your capability's repository (required) :
Usage: PatchPoint System Administrator's Guide: Chapter 3, page 34; Chapter 7, page 65
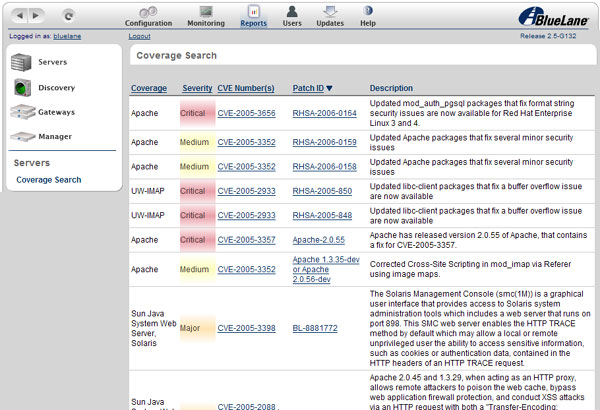
Within our product we have screens that show the mappings between the Vendor Patch ID and individual CVE numbers. These can all be accessed on an individual server (or set of servers) basis. Below we see what we refer to as a Profile of a set of Microsoft servers, their patches and the corresponding CVE numbers.

10) Documentation Indexing of CVE-Related Material <CR_4.4>
If your documentation includes an index, provide a copy of the items and resources that you have listed under "CVE" in your index. Alternately, provide directions to where these "CVE" items are posted on your web site (recommended) :
ActiveFix
- finding by CVE
CVE
- Coverage Search
- description of
- in reporting
patch
- finding by CVE
vendor patch
- finding by CVE
vulnerabilities
- finding by CVE
All documentation is available with an authorized Support account.
Candidate Support Questions
11) Candidates Versus Entries Indication <CR_6.1>
If CVE candidates are supported or used, explain how you indicate that candidates are not accepted CVE entries (required) :
Description of candidates vs. entries provided in PatchPoint System Basics Guide: Chapter 5, page 32: "About CVE"
CVE refers to the Common Vulnerabilities and Exposures (CVE) list of standardized names for publicly known security vulnerabilities and system exposures. CVE names are categorized by status as either "entry" or "candidate". An entry is a vulnerability or exposure that has been accepted to the CVE list. Candidate status (formerly identified with the prefix "CAN", such as "CAN-2005-0001") indicates that the reported vulnerability is under review for list inclusion. A candidate is not an accepted CVE entry, and there is no guarantee that it will become an official CVE entry.
Each CVE record includes the CVE name (e.g., "CVE-2006-0010"), status as either "entry" or "candidate", a description of the vulnerability, and links to other pertinent information.
A CVE name has two fields: the "CVE" prefix and a unique eight-digit number. Thus, if a CVE name reads "CVE-2006-0005," the unique identifier is "2006-0005".
The Blue Lane PatchPoint System utilizes CVE standardized naming as a searchable reference for those vulnerabilities and exposures being fixed by a vendor security patch; thus, by an ActiveFix inline patch where the PatchPoint System is deployed. For more on CVE, refer to cve.mitre.org .
12) Candidates Versus Entries Explanation <CR_6.2>
If CVE candidates are supported or used, explain where and how the difference between candidates and entries is explained to your customers (recommended) :
Description of candidates vs. entries provided in PatchPoint System Basics Guide: Chapter 5, page 32: "About CVE"
13) Candidate to Entry Promotion <CR_6.3>
If CVE candidates are supported or used, explain your policy for changing candidates into entries within your capability and describe where and how this is communicated to your customers (recommended) :
On a bi-weekly basis, we review any promotions of the CVE database and make appropriate changes to our product's CVE mapping database. This is communicated to our customers via Release Notes, which accompany the database/product updates.
15) Search Support for Promoted Candidates <CR_6.5>
If CVE candidates are supported or used, explain where and how a customer can find the explanation of your search function's support for retrieving the CVE entry for a candidate that is no longer a candidate (recommended) :
A user can locate a specific CVE by opening up the profile associated with the set of servers he would like to see. Once open all of the relevant CVE items would be accessible to him for his information. Since our product is Vendor Patch ID oriented, there are no specific tasks that the user must take on individual CVE numbers. But if interested, the user can look up the latest CVE numbers and see that he has coverage for those vulnerabilities on a per profile basis.

16) Candidate Mapping Currency Indication <CR_6.6>
If CVE candidates are supported or used, explain where and how you tell your users how up-to-date your candidate information is (recommended) :
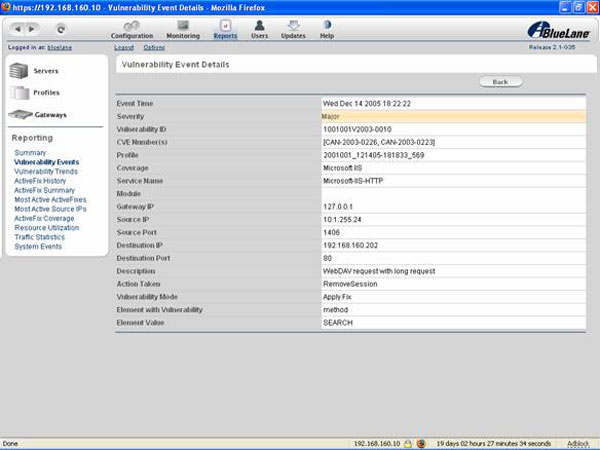
In our reporting tool, the CVE number associated with a particular vulnerability event is called out for informational use by the user:
Type-Specific Capability Questions
Media Questions
31) Electronic Document Format Info <CR_B.3.1>
Provide details about the different electronic document formats that you provide and describe how they can be searched for specific CVE-related text (required) :
We provide PDFs of all documents, and they are available on CD-ROM (packaged with each appliance) and on the website via Support login. Also, online help is provided with the user interface. In the case of both the Admin Guide and the online help, the topic "About CVE" can be found in the Table of Contents, and the term "CVE" is included in the Index.
Also, a list of security patches covered by the Blue Lane PatchPoint System is provided via Support login. This is a web page with multiple tables containing the Vendor, the Patch ID, the related CVE name (if it exists), and an original description of the mitigated vulnerability.
32) Electronic Document Listing of CVE Names <CR_B.3.2>
If one of the capability's standard electronic documents only lists security elements by their short names or titles provide example documents that demonstrate how the associated CVE names are listed for each individual security element (required) :
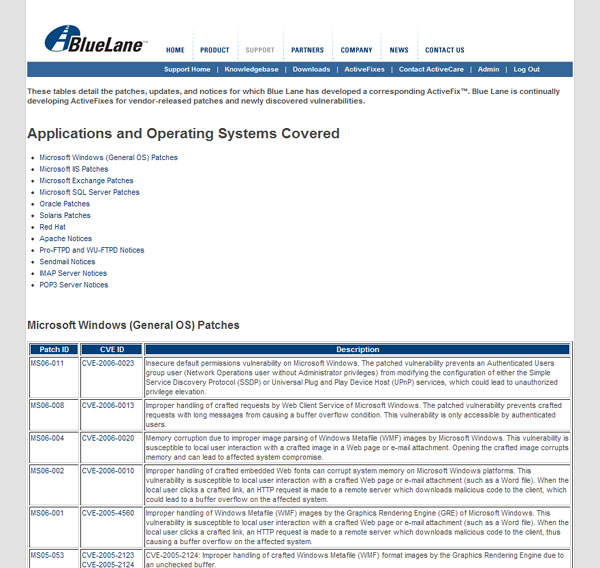
Below is a screen shot showing the patch coverage list that is available via Support login. All Patch IDs and CVE names are hotlinked.
33) Electronic Document Element to CVE Name Mapping <CR_B.3.3>
Provide example documents that demonstrate the mapping from the capability's individual elements to the respective CVE name(s) (recommended) :
See answer to 32 ( above ).
Graphical User Interface (GUI)
34) Finding Elements Using CVE Names Through the GUI <CR_B.4.1>
Give detailed examples and explanations of how the GUI provides a "find" or "search" function for the user to identify your capability's elements by looking for their associated CVE name(s) (required) :
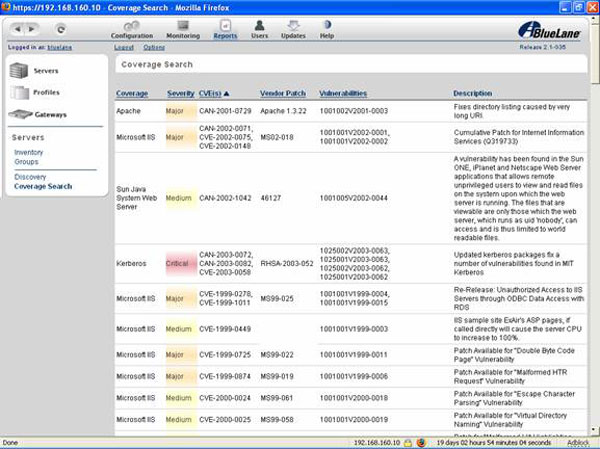
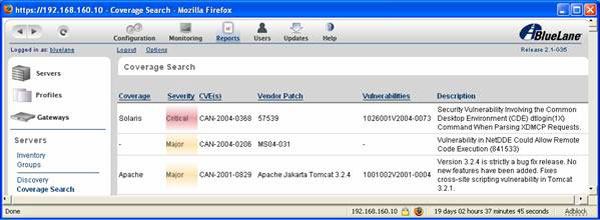
In the user interface, the "Coverage Search" feature maps CVE names to Vendor Patch IDs, or Vendor Patch IDs to CVE names as shown below. You either choose to search by CVE name or by Vendor Patch (ID).
35) GUI Element to CVE Name Mapping <CR_B.4.2>
Briefly describe how the associated CVE names are listed for the individual security elements or discuss how the user can use the mapping between CVE entries and the capability's elements, also describe the format of the mapping (required) :
The user searches by either CVE name or Vendor Patch ID to determine what coverage bucket (22 available - e.g., Apache, IIS, Oracle, Red Hat) to build a server profile around, specifically to protect a server behind the PatchPoint Gateway appliance.
The table format is as follows (see below):
- Coverage: The name of the application (i.e., Apache, IIS) as it appears in the UI when the user creates a server profile.
- Severity: Severity of the vulnerability as defined by the vendor
- CVE Number(s): CVE name related to the vulnerability. There may be multiple CVE names per Patch ID as some patches cover multiple vulnerabilities.
- Patch ID: ID of vendor patch that resolves the vulnerability
- Description: description of patched vulnerability as either the title provided by the vendor or a description developed by Blue Lane where a vulnerability title was lacking
36) GUI Export Electronic Document Format Info <CR_B.4.3>
Provide details about the different electronic document formats that you provide for exporting or accessing CVE-related data and describe how they can be searched for specific CVE-related text (recommended) :
Outside of the Coverage Search feature in the user interface, the coverage list available via Support login is the singular electronic document that lists all of the vendor patches covered by the PatchPoint System. Since this is a web page, the current method of searching for a CVE name is by using your browser's Edit > Find in this Page feature.
Questions for Signature
37) Statement of Compatibility <CR_2.7>
Have an authorized individual sign and date the following Compatibility Statement (required) :
"As an authorized representative of my organization I agree that we will abide by all of the mandatory CVE Compatibility Requirements as well as all of the additional mandatory CVE Compatibility Requirements that are appropriate for our specific type of capability."
Name: Matthew Rodgers
Title: Director, Product Management
38) Statement of Accuracy <CR_3.4>
Have an authorized individual sign and date the following accuracy Statement (recommended) :
"As an authorized representative of my organization and to the best of my knowledge, there are no errors in the mapping between our capability's Repository and the CVE entries our capability identifies."
Name: Matthew Rodgers
Title: Director, Product Management
39) Statement on False-Positives and False-Negatives <CR_A.2.8 and/or CR_A.3.5>
FOR TOOLS ONLY - Have an authorized individual sign and date the following statement about your tools efficiency in identification of security elements (required) :
"As an authorized representative of my organization and to the best of my knowledge, normally when our capability reports a specific security element, it is generally correct and normally when an event occurs that is related to a specific security element our capability generally reports it."
Name: Matthew Rodgers
Title: Director, Product Management
Use of the Common Vulnerabilities and Exposures List and the associated references from this Web site are subject to the Terms of Use . For more information, please email cve@mitre.org .
Copyright 2005, The MITRE Corporation . CVE and the CVE logo are registered trademarks of The MITRE Corporation.
For more information, please email
cve@mitre.org
.
Page last updated:
Friday, 09-Jun-2006 00:23:13 EDT